IOTA Under Fire For Reliance on User Seed Generation
IOTA has been making news recently as it has chalked up impressive partnership deals with partners including Bosch in Germany.
However, it is now been attacked on social media and by a number of users because of a particular issue that relates to its wallet security. This has already resulted in almost $4m in IOTA being stolen from holders.
The problem came from the fact that IOTA has had to rely on the users to create their own seeds for their wallets. This can be seen below in the instructions for the type of seed they require.
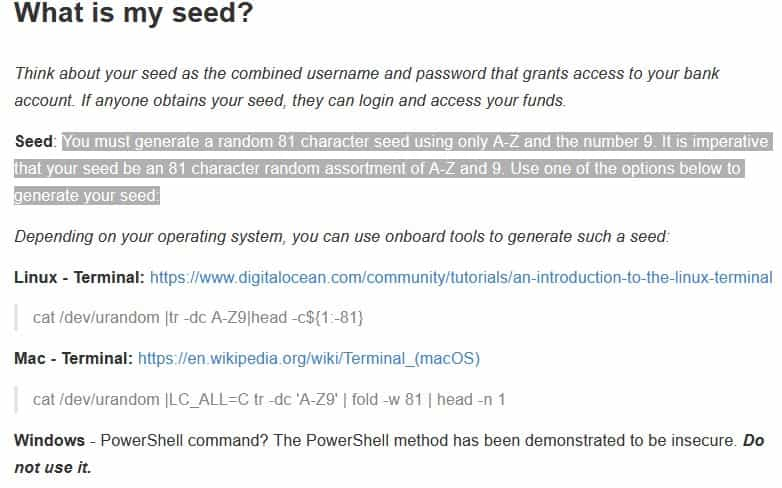
Instructions for Generating an IOTA Seed. Source: iota.org
For the more technically inclined users, this could be done using the command line tools described. However, many of the newer less technical users resorted to online seed generators.
Of course, this is something that the scammers know themselves all too well. This is where things went wrong for these unfortunate users.
The Power of a Seed

Fake IOTA Seed Generation Website
The seed words are arguably the most important pieces of data for any cryptocurrency. They are essentially the master keys to the safe that is your wallet. Hence, in the hands of someone else, your crypto is in their hands.
In the case of the latest IOTA seed scam, the hackers relied on the websites that created the seed phrases for use in the wallets. They had either created these sites from the beginning or they had taken over control of a legitimate website.
The hackers had successfully sucked up a great deal of wallet seed phrases from these crypto users. An example of one of these sites is iotaseed.io. When you visit the site in question you can see that the page has been taken down.
The Co-ordinated Attack
Given that the hackers now had all of the seeds for the unsuspecting victims, they had to strike and attack the unsuspecting victims. It appears that they chose Friday night as the most effective time to do this.
The hackers also wanted to make sure that they had effectively covered their tracks. Hence, they decided to launch a wide-scale Dedicated Denial of Service (DDoS) attack on some of the most used IOTA nodes on the network.
This DDoS effectively brought massive strain on the network for a period of time. This meant that the users were not able to stop the attackers and they were able to make a clean break with the stolen funds.
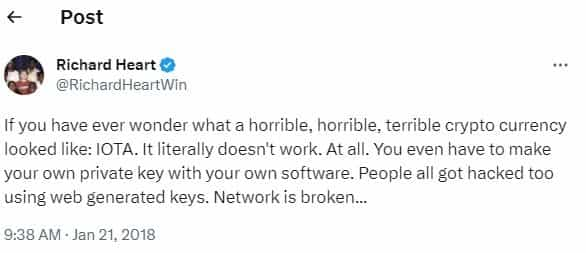
In total, the hackers were able to make away with a pretty sizable chunk of IOTA valued at just less than $4m at the prices prior to the hack. Clearly, there were those who were not happy with this as demonstrated by the below tweets.
The IOTA development team moved quickly to make sure that no one made use of these websites by issuing a PSA on Reddit. However, this came too late for many as their IOTA tokens started to flow out of their wallets.
User Error or Design Flaw?
While many in the IOTA community tend to agree that this was in essence a user error, one has to question the foresight of having a wallet that requires users to generate their own seeds. Such important information should not be left to fundamental error.
Moreover, this is not the first time that IOTA has faced criticism of its technology. The most notable example was the research that was done by an MIT team that disclosed the hashing function vulnerability.
When these were disclosed, the IOTA foundation actually threatened to sue the researchers and accused them of trying to needlessly attack the IOTA project.
This is unfortunate as these particular criticisms are helpful in improving security. The costs and efforts of addressing concerns in the community are much less than the damage caused by security issues such as this one.
Featured Image via Fotolia
Disclaimer: These are the writer’s opinions and should not be considered investment advice. Readers should do their own research.
