A Chinese company called Cheetah Mobile has a blockchain research arm that was able to find a vulnerability in two popular Cryptocurrency wallets.
The wallets in question are the Bitcoin.com and Jaxx Blockchain wallet. Cheetah mobile reached out to the wallet developers to let them know about the vulnerability. This also coincided with the release of Cheetah's very own Bitcoin wallet that is called "SafeWallet".
If the disclosure is indeed true, then this must have been quite a serious vulnerability. These wallets are no doubt some of the most popular on the market and are used by millions of users globally.
So what exactly was the vulnerability and how much risk were you in?
Bitcoin.com Wallet
In the case of the Bitcoin.com wallet, the mnemonic seed phrases were not encrypted before been stored. They were stored as a plain text version in the following directory “/data/data/com.bitcoin.mwallet”. This file exists on the phone's operating system and is hence local.
In order to get access to this seed phrase, all that would be needed is that some malicious application could attempt to gain "root access". This means that they would have privileged access to much of the phone's files.
Hence, all that the attacker would need to know is that someone is a regular Bitcoin user and that their wallet of choice is the Bitcoin.com one. They could get them to install the malicious application which would give the hacker root access and thereby able obtain the seed words.
For those who don't know how cryptocurrency wallets work, these seed words are used to unlock your private keys. Once the attacker has access to this they can siphon off your funds in a heartbeat.
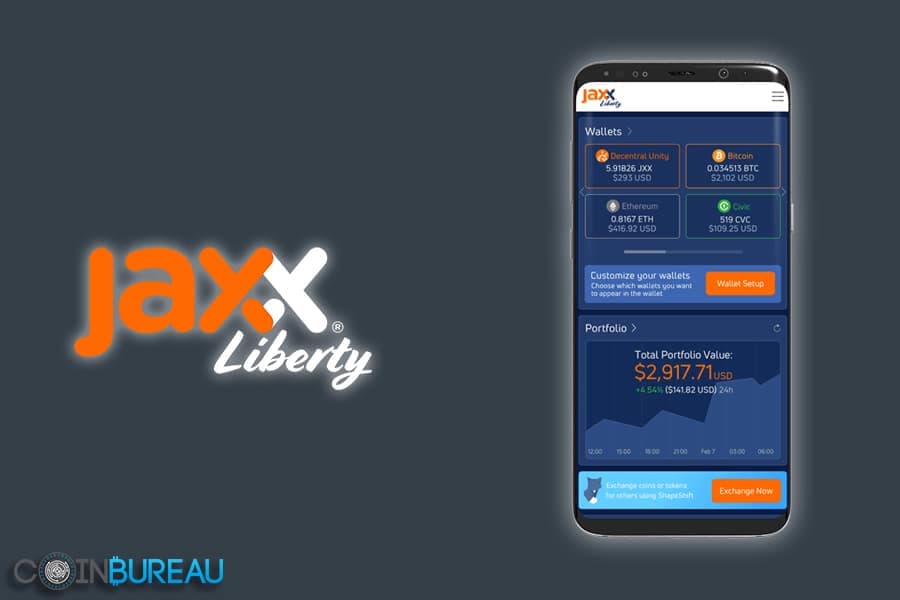
Jaxx Blockchain Wallet
In the case of the Jaxx wallet, the private key was better protected. The key was put through an AES algorithm which is one of the most secure methods to encrypt data. This is also used by a number of US government agencies to secure their messages.
However, even though the Jaxx developers had properly encrypted the private keys, the implementation of the AES encryption algorithm was in the code base of the application. This means that the encrypted private keys could still be useful for a hacker.
Given that the hacker now knows how to decrypt the private keys, they can easily do so on another device. Now with private key effectively decrypted, they can use it to access your wallet and drain your funds.
This is not the first time that someone has highlighted issues with the Jaxx Bitcoin wallet. For example, researchers at Techgage have found that Jaxx stores user information in the %APPDATA% folder. This user information is the all that is required in order to re authenticate the wallet.
Therefore, if someone was able to get access to your PC as well as the APPDATA folder then they could just authenticate this on another computer and re open your wallet. With this user data, they can effectively sign transactions and send your funds out.
What is The Cheetah Wallet?
 Image via wikipedia.org
Image via wikipedia.orgGiven that the researchers at Cheetah Mobile were able to discover these vulnerabilities as well as disclose it to the other developers, one would expect them to have a great mobile wallet solution.
The Cheetah Mobile team has released an extensive white paper where they detail the most important considerations for a choosing the right mobile wallet. They took a number of these best practices and incorporated them into their own proprietary SafeWallet.
The SafeWallet makes use of "unique three tiered" security defence system. They want to try and protect the user in three key ways which include user behaviour, asset management and phone security. The wallet currently supports Bitcoin and Ethereum with further currency support on the way soon.
Interestingly, the wallet will also include an algorithm that will optimise the transaction fees. This could be helpful for those new users who are not too familiar with Bitcoin transaction fees and Ethereum gas pricing.
Safewallet is still a new wallet which means it needs time to prove itself before it can be used for storing larger amounts of coins. Yet, their research into the other vulnerabilities at far more popular wallets should add to their credentials.
Featured Image via Fotolia