Wallet Warning: SpriteCoin Installs Ransomware on User's Devices
There is currently a cryptocurrency application that is promising to make its users really wealthy. However, when users install the infamous SpriteCoin wallet, they will have surrendered their files to ransomware and much more.
This was first discovered by researchers at fortinet. In their report, they took a look at the application in question and identified the malware.
Once the user has installed the wallet on their PC, the application identifies files that they would like to encrypt. The wallet then quickly encrypts the files in question. Moreover, once they have made the payment, the malicious code still remains on the PC and performs other tasks.
Let's take a deeper look into the report...
How Does it Work?
The attack will most likely begin with some form of social engineering vector. This is because it will rely on the user to download the .exe file themselves.
These could take the form of some email purporting to offer an amazing opportunity to claim a new coin. It could also come from some malicious website or landing page offering quick returns.
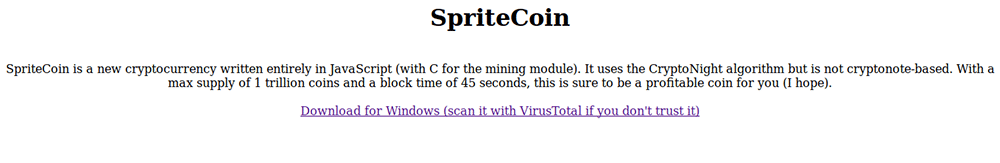
Once users are hooked and decide that they want their new coins, they are taken to a page like the one below.
Once the user has downloaded the file and they open the executable, they are prompted for a password in order to initiate the "setup". The next screen will present them with a "downloading blockchain" description.
Unbeknownst to the user, the ransomware is connecting to a Tor site via a proxy. It will then start scanning the PC for any files with a range of different extensions including all word documents.
It won’t only encrypt the files of the user but it will relay a great deal of credentials of the user through the proxy and eventually to the Tor site. The researchers stated
The ransomware first looks to harvest Chrome credentials, and if it finds nothing it then moves on and tries to access the Firefox credential store
This information will no doubt be very helpful to the hacker. There is also a relatively high chance that the victim has invested in other cryptocurrencies which means the data is that much more valuable.
Decrypting the Files
As this is a Ransomware attack, it would have to alert the user to the fact that their files have been encrypted. They would also require the user to pay in order to decrypt their files. Below is the window that the users will be presented with.
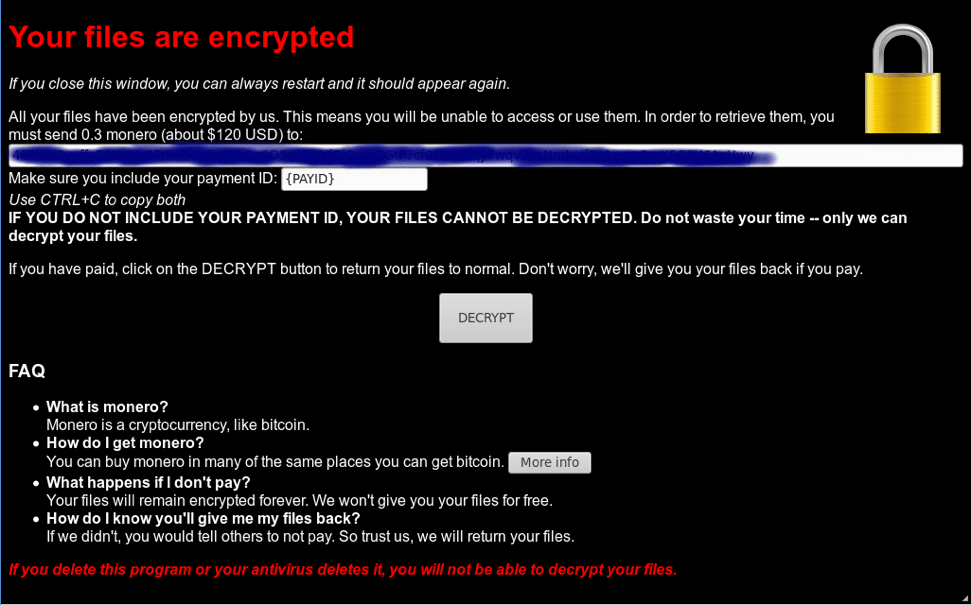
What is interesting is that unlike other high profile ransomware attacks, they are not asking for Bitcoin but rather Monero. This is not entirely unsurprising as privacy conscious crytpocurrency cannot be traced by the authorities.
One may think that the hackers would merely decrypt the files and leave the victim in peace?
This is unfortunately not the case. Once the users begin the decryption phase, the program will download another malicious payload. The researchers were not able to fully analyse it but it seemed to contain code that would activate webcams and parse security certificates.
Always Think Twice
This clearly demonstrates the virtues of thinking twice before acting. The hacker relied on the victim's complacency and greed to download the malicious ransomware.
For example, we have seen exit scams take place in the ICO market as well other prominent ponzi schemes. Hackers are able to exploit the greed and FOMO (Fear of Missing Out) of most new users to cryptocurrency.
Even if are not being tempted with a juicy offer, hackers will using phishing in order to trick you in handing over your credentials. Something that may be routine could turn out costing you dearly.
Cryptocurrency security coupled with generous doses of scepticism will help you greatly.
Disclaimer: These are the writer’s opinions and should not be considered investment advice. Readers should do their own research.
