Loki is another privacy coin that has recently been attracting a fair bit of interest in crypto circles.
This is a privacy conscious cryptocurrency that which joins a long list of similar coins that are trying to take advantage of Bitcoin's lack of privacy. Indeed, one could be forgiven for feeling slightly overwhelmed by the sheer number of projects developing privacy centric blockchains.
In this environment, can Loki really stand out and carve a niche for itself? Or will it come and go like similar other privacy coins?
In this Loki review, we will take an in-depth look at the project. We will analyse the underlying privacy protocols and technology as well as delve into the team experience, user adoption potential and long term LOKI token prospects.
What is Loki?
Loki was created as a fork of Monero, which is already one of the most anonymous and private cryptocurrencies. With Loki, the developers are looking to create a completely anonymous, private, secure network for communication and trade.
Trade and Communicate with Absolute Freedom
So how then does Loki differentiate itself from Monero? In several ways actually.
First of all, the Loki team is not competing with Monero. It simply uses Monero’s privacy features to create a foundation for its second service layer of Service Nodes. The Service Nodes utilize an architecture that is similar to other private internet protocols to allow private communications on the Loki network.
 Main Features of Loki. Source: Loki Website
Main Features of Loki. Source: Loki WebsiteIt’s these peer-to-peer protocols that help to create the decentralized network for routing traffic over the internet in a private fashion. Monero uses ring signatures and stealth addresses to create plausible deniability for its users when signing transactions.
A ring signature works by creating a ring of signers, where all but one is just a decoy. While Loki uses ring signatures in the same way as Monero, it also improves on Monero by enforcing a minimum ring size of 10, where Monero has a minimum ring size of 5.
Stealth addresses also ensure that the public key of the receiver of a transaction never gets linked to their transactions. These work by creating a one-use stealth address every time a transaction is sent on the Loki network.
The funds are sent to this address and the receiver calculates a private spend key for this address, allowing them to take ownership of the funds without revealing their own public address. This anonymity for receivers is one of the core features of the Loki network.
Loki Technology
Of course, in order for Loki to adequately differentiate itself from other privacy coins, it has to have some of its own unique technology. Below are some of the features that were exclusively included in the Loki network.
Mixin Distribution
As mentioned above, ring signatures typically contain the true unspent output being sent and a number of decoys. These decoys are called mixins. They look like unspent outputs, but are not necessarily so.
 Ring Signatures with "Mixins" included in Transaction. Source: Cryptonote
Ring Signatures with "Mixins" included in Transaction. Source: CryptonoteLoki samples mixins based on user spending habits, which means a third-party can’t ever assume the oldest mixin is a decoy, because the distribution of chosen outputs reflects the possibility of an older unspent mixin being included in the ring signature. This sampling was included to increase the network defenses against a temporal association attack.
Service Nodes
A great deal of of the functionality and network scalability is enabled through the use of the Service Nodes. These are the staking component of the hybrid Proof-of-Work and Proof-of-Stake consensus model on the Loki network.
In order to operate one of these service nodes, the node operator has to time lock a certain amount of their LOKI tokens in return for a portion of the block rewards. This is provides the Loki network with protection against Sybil attacks using market based incentives.
The idea of using market based incentives to prevent Sybil attacks was first theorized by DASH and the use of their masternodes. Essentially, as an attacker tries to gather more of the coins in order to control the network, the price of outstanding supply will increase and make the attack prohibitively expensive.
Hence, to reduce outstanding supply Loki encourages the running of these Service Nodes. There are significant staking requirements to become a Service Node, which not only encourages honest behavior but also reduces outstanding supply.
The Service Nodes also fulfill another important function on the Loki network as they are capable of creating Service Node Applications (SNApps) to serve and store private messages.
Loki Messenger
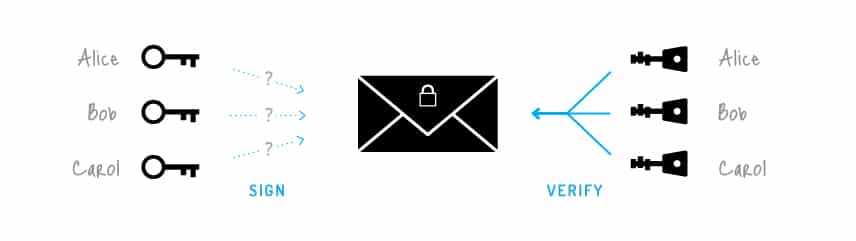
The very first SNApp planned for the Loki network is a decentralized, private, encrypted messaging service called Loki Messenger. While there are already private messaging applications these are all built using centralized servers that can be the target of a third-party attack. In the case of Loki Messenger, public-private key cryptography is used to maintain privacy.
The receiving address will be a Loki holder’s public key. The sender broadcasts their message to three randomly selected Service Nodes, and it is signed with the receivers public address. Each Service Node can hold messages for up to 24 hours in their “message pool”. Messaging functionality is planned to be available in the Loki wallet software, as well as via a mobile application.
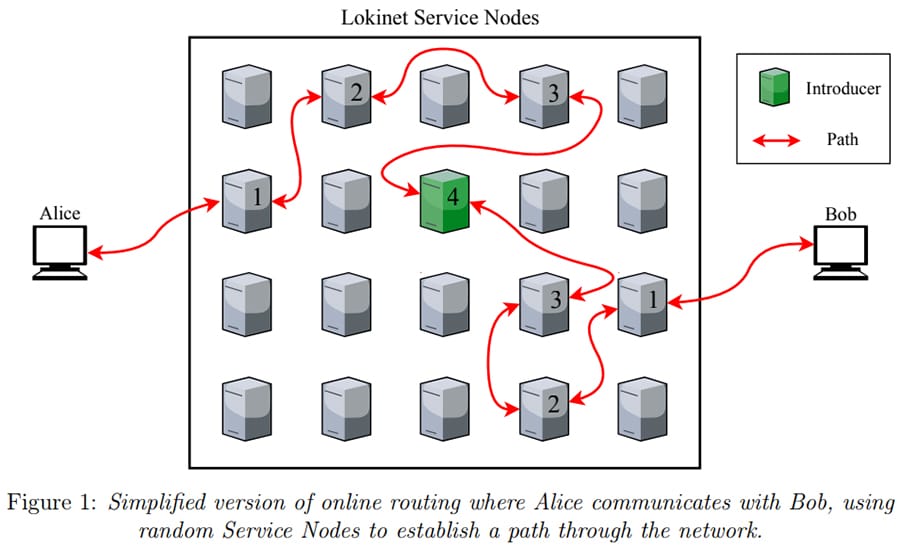 Online routing in the Loki Network where Alice Communicates with Bob. Source: Whitepaper
Online routing in the Loki Network where Alice Communicates with Bob. Source: WhitepaperYou’ll find two unique encryption features as part of Loki Messenger:
- Perfect Forward Secrecy: Loki Messenger uses a brand new shared encryption key for each message sent. This avoids attacks where a long term key is exposed because revealing one key from Loki Messenger will not compromise the entire message chain. To break the encryption of a message chain an attacker would need to find the key for each individual message, which is extremely difficult and unlikely.
- Deniable Authentication: This allows two parties to prove they are the sender and receiver, but prevents any third party from discovering the true sender or receiver of any message.
Lokinet for Anonymous Browsing
Loki has also created a novel type of mixnet, something similar to Tor or I2P in some ways, to prevent Sybil attacks and is calling it Lokinet. This new type of mixnet uses a market-based Sybil attack resistance. Lokinet combines that with onion routing to create a new private tunnel to access the internet.
Onion routing means that each node only knows where they received a data packet from and where they sent it on to. They do not know the origin of the packet, meaning they don’t know your location or who you are. By using Lokinet, you will be able to access the Loki SNApps and any website you like without revealing your IP address and location.
The decision was made to create a brand new mixnet rather than using existing mixnets because neither Tor nor I2P have been able to fully mitigate Sybil attacks. Additionally, the Tor network is quite centralized, while I2P has a weak consensus model and no formal way to access the internet anonymously.
Lokinet will use distributed hash tables built from staking transactions, which will give Service Nodes permission to act as routers on the network. Lokinet will maintain high standards of service through its decentralized registration and de-registration, where Service Nodes are evaluated by consensus and can be removed if not up to minimum standards regarding bandwidth, message storage and blockchain storage.
You can learn more about Lokinet here.
The Loki Team
The Loki website lists 4 executive team members, 10 developers, and 8 supporting organizations.
 Members of Loki's Executive Team
Members of Loki's Executive TeamBy some accounts the most impressive team member is lead developer Tom Winget, who was previously a huge contributor to Monero in 2014 and 2015. His experience has been vital to the development of Loki.
The Founder of Loki is Simon Harman, who has a background in web development and project management. He is also a member of Australia’s Blockchain Center, which is the country’s largest community of blockchain entrepreneurs, experts, mentors and investors.
LOKI Token History
Loki conducted a private sale of tokens in March 2018, selling 15% of the 150 million total token supply at $0.68 and raising $9 million. The remaining tokens will be held for mining rewards, but there was also a large airdrop held following the private sale. There was never a public ICO for Loki.
After the airdrop the price of LOKI dropped throughout most of 2018, reaching a low around $0.13 in August 2018. It has been rallying since then, and as of late October 2018 is trading at $0.4433 per LOKI. That gives it a market cap of nearly $13 million and makes it the 301st largest coin by market cap.
 LOKI Token Price Performance since Launch. Image Source: CoinMarketCap
LOKI Token Price Performance since Launch. Image Source: CoinMarketCapIf you’re looking to buy LOKI you can only do so at Cryptopia or TradeOgre. There are no other exchanges currently supporting LOKI.
Storing LOKI must be done in the official Loki wallet available on their website for Windows, MacOS and Linux. The wallet not only allows storage of LOKI, but also opens up the possibility of mining LOKI and beginning to use the system for trading and eventually sending and receiving private messages.
Conclusion
As a privacy coin Loki has made several improvements over Monero, but I’m not certain that’s enough to recruit the Monero faithful. Indeed, you can see how the price of LOKI tokens suffered following the conclusion of the airdrop, although they have been making a strong comeback lately.
Those interested in private messaging will certainly be interested in Loki Messenger, but until the platform can begin to deliver more SNApps I’m not sure the messenger alone is enough to garner widespread adoption.
There’s also the question of exchange support. With only two exchanges offering LOKI it’s very difficult for the coin to gain traction. Unless some of the major exchanges such as Binance, OKEx and Huobi pick up LOKI I can’t see how it will gain additional traction.
I like the concept and the plans of the team, but the token needs better marketing or it could very well end up lost in the obscurity of the host of other privacy and messaging coins being developed.